Hello world, welcome to haxez where today we’re looking at the last realistic 16 web application mission from Hack This Site. This mission was difficult for all the wrong reasons. It wasn’t because it was designed in a challenging way. No, it was because it uses Adobe Flash which has been dead for a while now. The challenge itself was a lot of fun despite the technical problems encountered along the way. I don’t know why I’m complaining honestly, I learned an additional nugget of information along the way.
Realistic 16 Introduction
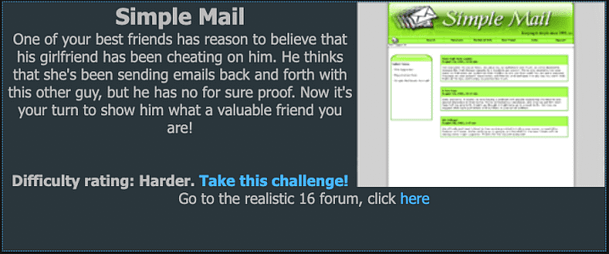
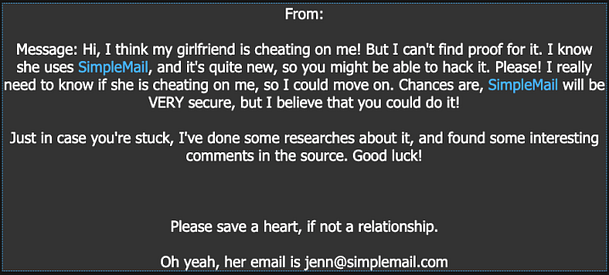
We receive a message from someone who neglected to leave their name. The message explains that they suspect that their girlfriend is cheating on them. Furthermore, they have noticed that their girlfriend is using simplemail.com a lot. They suggest that it could be the way his girlfriend is messaging her secret lover. We’ve been asked to hack in to simplemail and read his girlfriends emails. Not trying to be a warrior of virtue or anything but under normal circumstances this would be a pass from me.
Exploring The Realistic 16 Web Application
Upon navigating to the application we’re greeted with a lovely lime green decore that is reminiscent of the old KazaA downloading application. During the Degeneration X days of the internet, Limewire and KazaA were the go to downloading applications. Alas, The application has a number of options that allow you to register, login, search and perform other activities. I genuinely like the look and feel of this application.

Scouring The Source
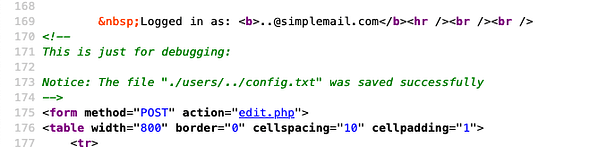
First things first, lets view what’s under the hood of this beautifully decorated vintage application. It’s mostly just what you would expect. However, there are a few comments that jump out at me. As you can see from the screenshot below, there is a comment that mentions an admin login. Lets head over to the URL and see what’s occurring.
https://www.hackthissite.org/missions/realistic/16/index.php?module=admin_login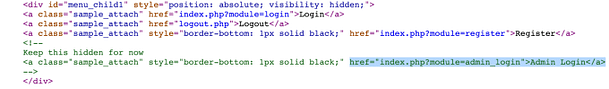
Deadend or Detour?
Well that’s not something you see everyday. The login page uses Adobe Flash which hasn’t been supported by browsers since *googles it* December 31’st 2020. Ok, it hasn’t been dead that long but it’s surprising how Adobe Flash already feels like a relic of the ancient internet.
As we know, most browsers don’t support Adobe Flash anymore. I tried to install an older version of Firefox first to get it working but didn’t have much luck. After a bit of googling, I stumbled upon the miracle that is Ruffle. I did try a number of other plugins first but none of them seemed to do the trick. Ruffle however, was amazing and did it’s job perfectly.
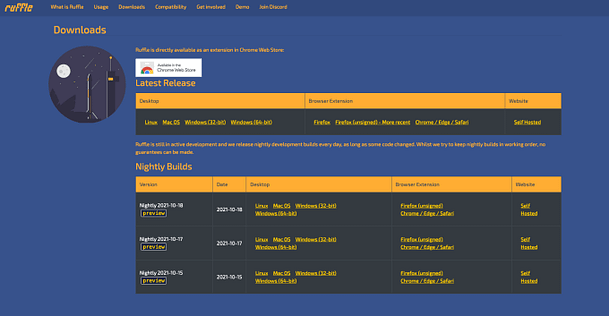
Web Browser Meet Ruffle
As Ruffle isn’t on any of the default plugin stores for the popular browsers yet, you need to download it and add it yourself manually. In order to do this in the Firefox web-browser you need to head to about:debugging in the URL. Then click This Firefox, and then select Load Temproary Add-ons and navigate to the file you downloaded. With that file loaded, we should now be able to access the URL.
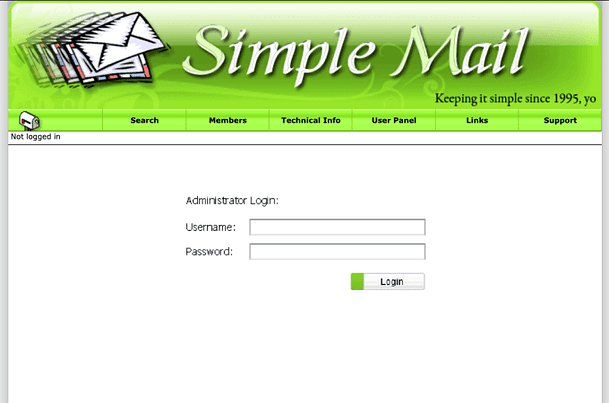
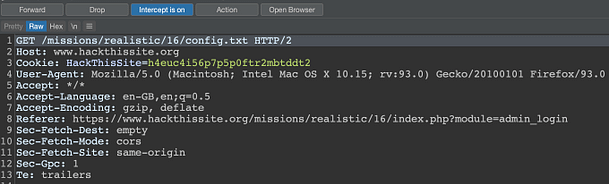
Realistic 16 Intercepting Web Requests
Before you continue, make sure you have your favorite web application penetration testing tool (Burp Suite) open and configured to intercept traffic. Then populate the Username and Password forms with test data and click submit. Inspec the request as it comes in to Burp and you will notice it is sending a GET request to a config.txt file. This suggest to me that the login form is checking something inside the config.txt before attempting to authenticate us.
Registering For Web Mail
Now we know a little bit about how the admin login works, lets register our own account and see if there is anything interesting there. I registered the user of test with the password of test because who cares about username and password complexity requirements anyway. Upon logging in, I had a look around and noticed that we had the ability to edit our profile. If we view the page source of this application we notice that it links to an edit.php page. If we click the link for edit.php to view the source of that page we notice that our profile configuration is stored in the following location /users/username/config.txt

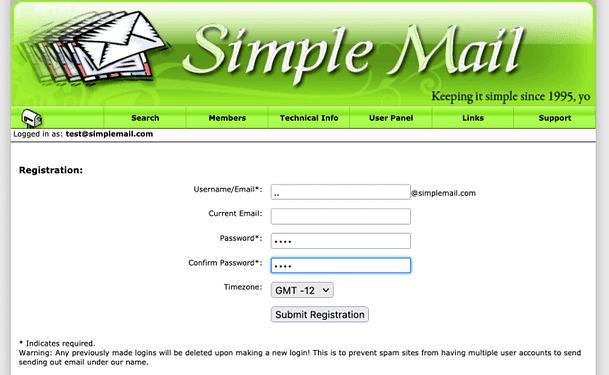
Registering A Diretory Traversal
We know that our profile is stored in config.txt and that the admin authentication script was checking a config.txt file in the root directory (a directory, or two? above us). Perhaps we can register a user with a directory traversal for the username so that when we edit our profile, we end up editing the admin config.txt. Well, that’s exactly what we need to do. Logout and head to the register page and register a user with the username ‘..‘. You will get an error message saying it was unable to create the email address, but you will get a conflicting messaging saying the registration was a success.
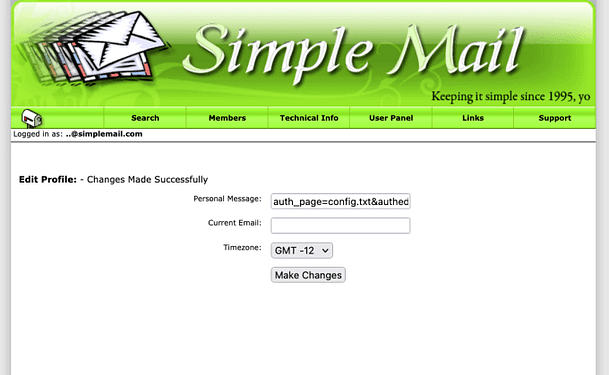
Admin Authenticiation
With our newly created user, we need to head back to the edit profile page. This time we’re going to use the edit profile to edit the config.txt file in the root directory. We need to input the following value in to the ‘auth_page=config.txt&authed=true&‘ which is going to allow us to authenticate.
Admin Access
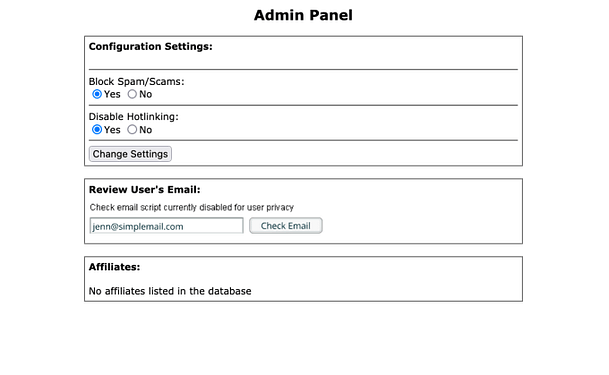
Ok, now that we have done that. Logout and head back to the admin URL and login with the other account we created. I used username test and password test. We shouldn’t revive an error message this time. Instead we should be redirected to the admin panel. The admin panel has a number of options including one that lets us read users emails. However upon submitting our clients girlfriends email address, we get an error message saying that the feature has been disabled for user privacy.
F**king Flash!
If we view the page source again we can see that this “Check Email” functionality is being provided by another Flash .swf file.
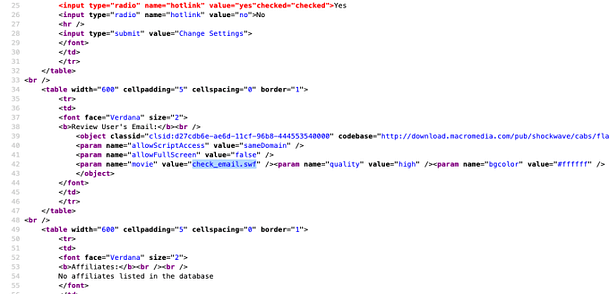
This is the part where we need to switch to our Linux Virtual Machine. We need to run a wget on the file and then disassemble it to see what’s going on. Fire up your linux terminal and run the following wget command. However, if you run in to errors advising you that the HackThisSite SSL certificate has expired (like I did), then you will need to tell wget to skip SSL checks. I will let you google that one.
wget https://www.hackthissite.org/missions/realistic/16/check_email.swf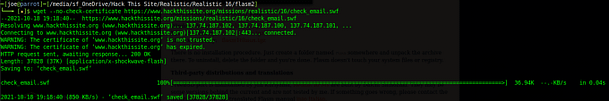
Realistic 16 Dissasembling Flash
Now we need to disassemble the Flash file, to do this I used the tool swfmill to convert it to an XML file. Once the Flash file is an XML file, we can look through it to find out why it isn’t letting us check users emails. Or better yet, we can find how it would check the users emails and we can use that instead. The command to convert the SWF to XML is as follows:
swfmill swf2xml check_email.swf test.xmlYou can then grep the XML for PHP and and you should find the following reference in the file.
/check_email.php?auth=true&id=63a4bf12cd&email=With some minor adjustments, we can append the link to the Hack This Site URL and solve the challenge.
https://www.hackthissite.org/missions/realistic/16/check_email.php?auth=true&id=63a4bf12cd&email=jenn@simplemail.comAnd that’s it, you have now completed the final realistic mission of the series, congratulations. On to the next set of missions.