Hello and welcome to haxez where I try to simplify CyberSecurity. This post is a walkthrough of the Hack This Site Basic 6 web challenge . If this is your first time here you can read the previous posts here: Part 1, Part 2, Part 3, Part 4, and Part 5. This challenge is about reverse-engineering the Basic 6 encryption mechanism that Sam is using to encrypt his password.
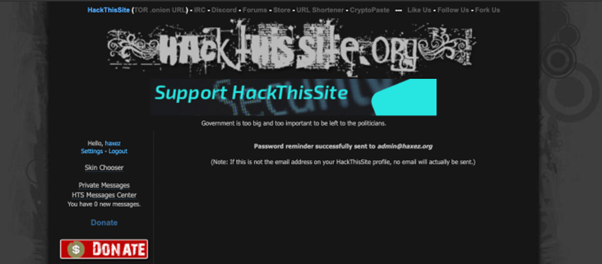
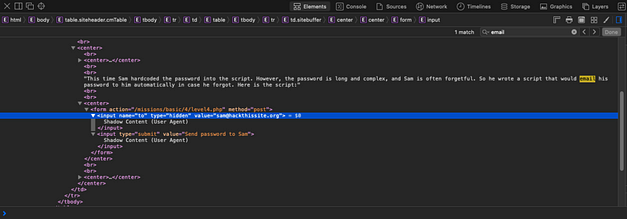
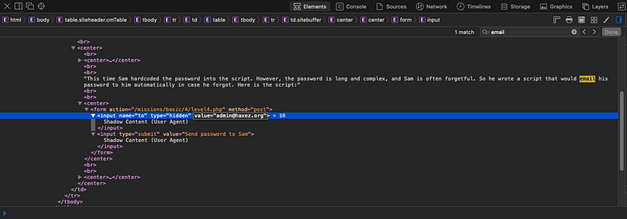
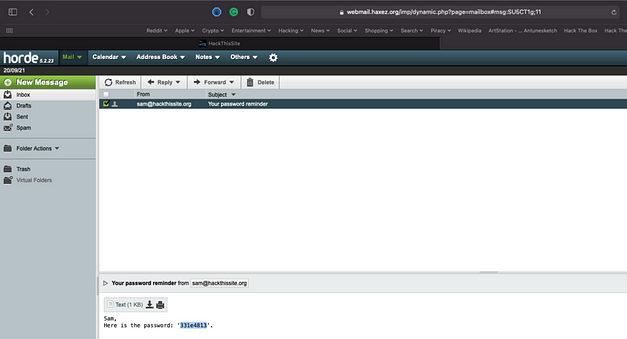
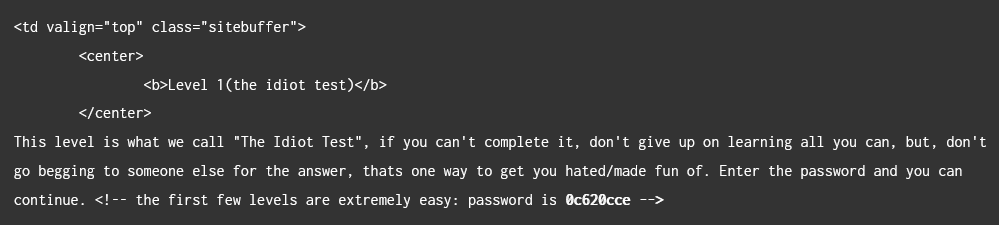
After logging in, you will see the following screen which reads. “Network Security Sam has encrypted his password. The encryption system is publically available and can be accessed with this form”. There is also an input box, which lets you test out the encryption mechanism. In order to test the mechanism, we need to feed it some data to see how it transforms it.
Basic 6 Web Encryption Mechanism
As you can see from the output below, the mechanism has converted 11111111 to 12345678. This allows us to deduce, that the encryption mechanism is adding 1 to a base value of 0. It is then incrementing that value and applying it to the submitted value. Essentially, the first character remains the same. The second character is increased by 1. Then, the third character is increased by 2 and so on and so forth.
However, the password contains non-alphanumeric characters such as semicolons and an equals sign. These non-alphanumeric characters, can’t be increased using simple arithmetic. They must be being converted to their ASCII decimal values before being put through the algorithm. We can test this by feeding the mechanism some special characters and seeing what happens.
As you can see from the results below, it is incrementing the non-alphanumerical characters too.
The inputted value of ‘!!!!!!‘ becomes ‘!"#$%&‘(‘. This does appear to confirm my theory, that it is converting the inputted value to the ASCII decimal value. Then, for every character in the string, the value is incremented by its position in the string starting from 0. It then converts it back from ASCII decimal to a human-readable format.
Bash Scripting the Solution
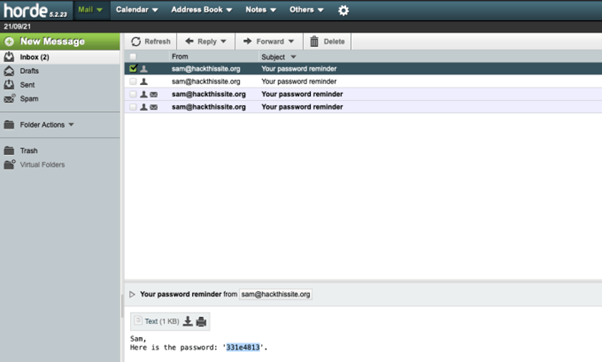
In order to solve this challenge, I wrote a basic bash script that reverses the encryption process. It takes the string and converts each character to its ASCII decimal value. It then subtracts 0 from the first character and loops around increasing the value to be subtracted by 1. Once the subtraction is complete, it converts the ASCII decimal back into a human-readable format, giving you the original password.
#!/bin/bash
# This is a script that will solve the password challenge of Hack This Site basic level 6.
# The password is dynamically generated so please replace the value of MyString with the password.
MyString='62cf4;j=' #replace this value
i=0
base=0
echo "Converting to ascii value"
while (( i++ < ${#MyString} ))
do
char=$(expr substr "$MyString" $i 1)
for j in `printf "%d" \'$char` ; do
j=$((j+base))
printf \\$(printf '%03o' $j)
base=$((base-1))
done;
done;
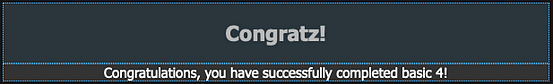
You can copy the script below and save it as decrypt.sh. You will then need to modify the permissions so that the script is executable. This can be done by running chmod +x decrypt.sh. You can then run the script by typing ./decrypt.sh in your terminal and it will output the correct password as you can see below.
─[joe@parrot]─[~]
└──╼ [★]$ ./decrypt.sh
Converting to ascii value
61ac06d6
All you now need to do is to take the output string and paste it into the password submission system and you will complete the challenge.
That’s all from me today. I apologise if my explanation of the encryption and decryption mechanism was a bit hard to follow.